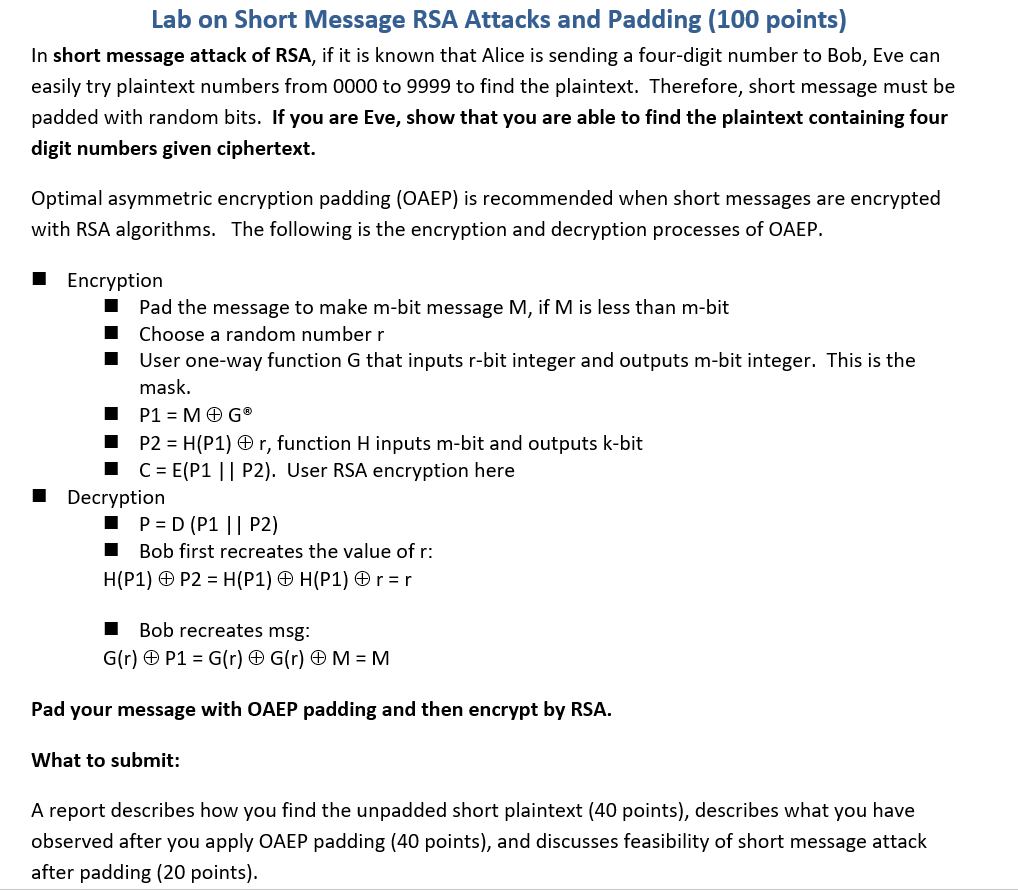
Remote Sensing | Free Full-Text | CGAN BeiDou Satellite Short-Message- Encryption Scheme Using Ship PVT

Remote Sensing | Free Full-Text | CGAN BeiDou Satellite Short-Message- Encryption Scheme Using Ship PVT

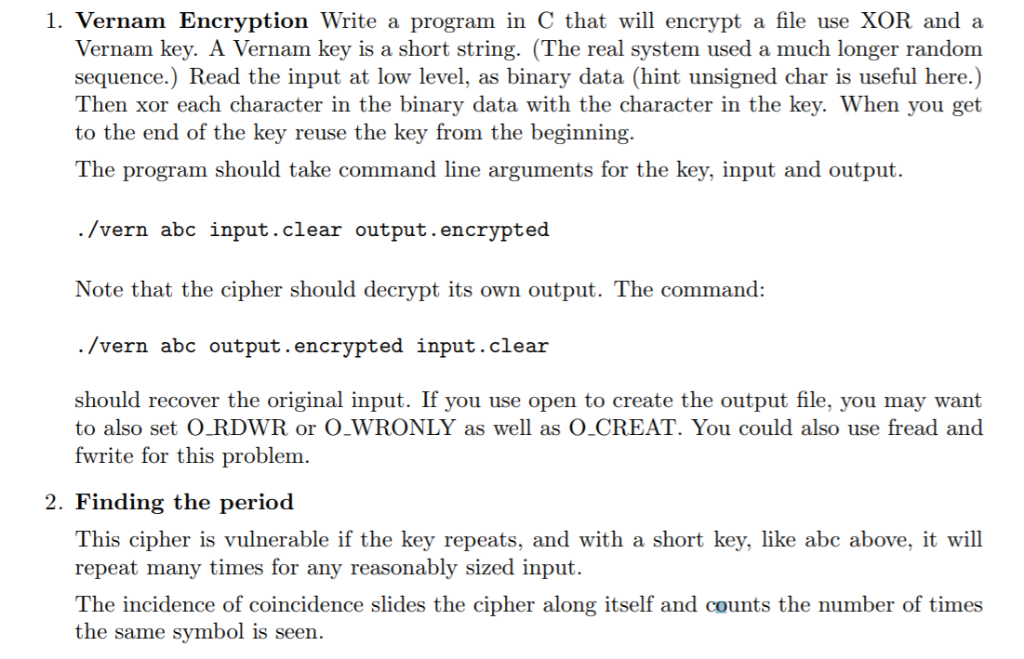
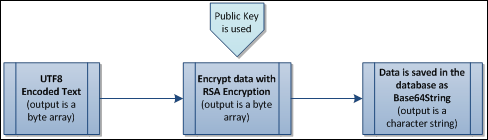
Design and Implementation of End to End Encrypted Short Message Service (SMS) Using Hybrid Cipher Algorithm

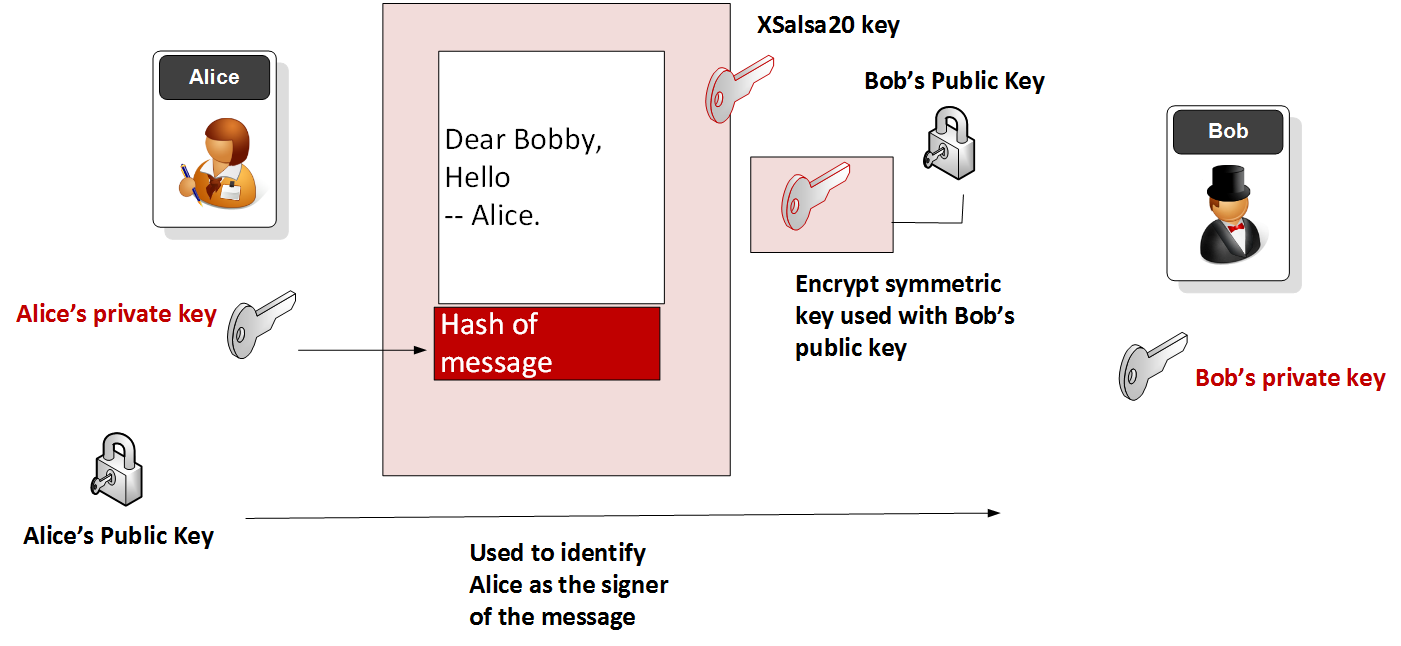
Figure1 shows the overall framework of encryption and decryption of the... | Download Scientific Diagram